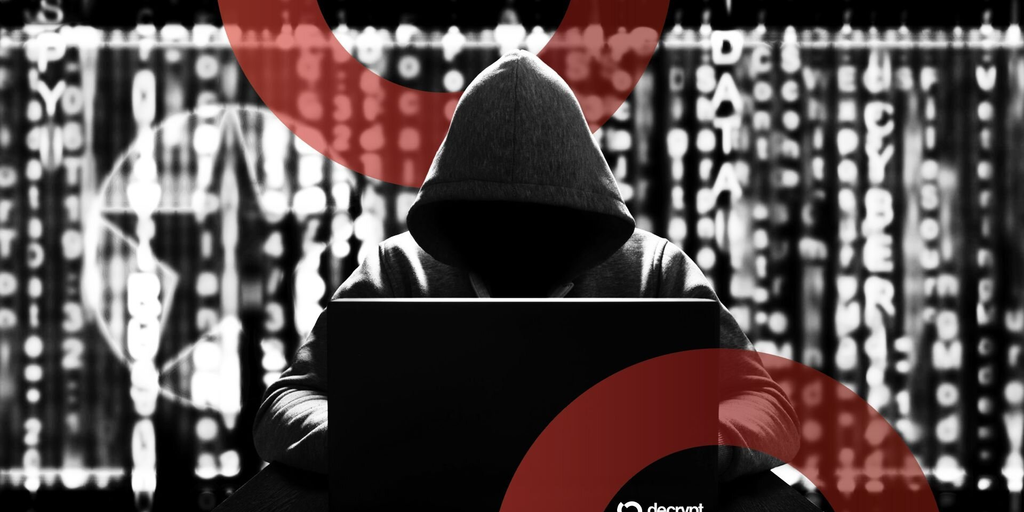
'We Are Ready to Speak': Drift Beckons North Korea-Linked Hackers Following $285M Exploit
The Solana-based project reached out to wallets holding stolen funds on Ethereum.
In brief
-
The team behind Drift, a Solana-based decentralized exchange, signaled on Friday that it wants to negotiate with hackers linked to North Korea.
-
If the funds were actually stolen by a state-sponsored group, the odds of recovery are zero, according to Curve Finance founder Michael Egorov.
-
The on-chain messages sent by Drift’s team provoked a response from a seemingly random wallet holding $200 worth of Ethereum.
Finding the group or individuals that stole $285 million worth of crypto from Drift earlier this week may be a tough task in the real world, but the team behind the Solana-based decentralized exchange knew exactly where to find its attackers on-chain.
On Friday, Drift said in a post on X that it had sent messages on Ethereum’s network to four wallets holding massive amounts of stolen crypto, which several security experts have begun linking to the Democratic People’s Republic of Korea: “We are ready to speak.”
The so-called Hermit Kingdom isn’t exactly known for negotiating with projects that its elite hackers siphon funds from, considering that bad actors linked to North Korea have absconded with $6.5 billion worth of crypto in recent years, according to blockchain security firm Elliptic.
Critical information of parties related to the exploit have been identified. Drift is now sending an on-chain message from 0x0934faC45f2883dd5906d09aCfFdb5D18aAdC105 to the ETH Wallets that holds the stolen funds.
Wallet 1: 0xAa843eD65C1f061F111B5289169731351c5e57C1 (Timestamp…
— Drift (@DriftProtocol) April 3, 2026
Still, the messages indicated that the true identity of whomever facilitated one of the biggest exploits in decentralized finance so far this year may not be truly known yet. That’s because the messages focused on the discovery details associated with attackers’ identities.
“Critical information of parties related to the exploit have been identified,” the on-chain messages sent by Drift’s team read. “To the community, Drift will share further updates as soon as third-party attributions are completed.”
When millions of dollars in crypto get swiped from a DeFi project, on-chain negotiations are a common course of action. Sometimes they work. Several years ago, someone who stole $600 million from Poly Network “for fun” returned the funds after a lengthy dialogue, for example. Oftentimes, attackers ignore any outreach and associated legal threats.
The probability of seeing Drift’s funds returned if North Korean hackers are involved is zero, according to Michael Egorov, founder of decentralized exchange Curve Finance.
“They never cooperate and they are not afraid of law enforcement,” he told Decrypt.
However, if the funds weren’t swiped by a state-sponsored group, then there is a chance that they'll be returned, he said. If the attackers’ identities are revealed, then he said that the “probability of them returning funds jumps to almost 100%.”
Ergorov noted that “maximal extractable value” traders can be an exception to the rule. With a strategy that focuses on essentially front-running users’ transitions to make profitable trades, they can occasionally step in front of hackers trying to abscond with funds.
“When they do, they return funds more often than not,” he said, adding that they sometimes hold onto some as a bounty, or leave it up for projects to determine.
Drift signaled earlier this week that the exploit, which has affected projects throughout Solana’s ecosystem that had built dependencies on the decentralized exchange, stemmed from “sophisticated social engineering.” The attackers were able to gain administrative control over the platform’s security by accessing two private keys.
Elliptic pointed to the attackers’ on-chain behavior and laundering methodologies as factors that led them to believe that hackers linked to North Korea were involved. Still, other security experts suggested that the attackers may have had some degree of insider knowledge.
It’s unclear who Drift believes the hackers could be, as well as whether the decentralized exchange is willing to offer them a bounty. Nonetheless, its attempt to retrieve funds on behalf of itself and the DEX’s users are public for all to see.
Decrypt has reached out to Drift for comment.
Someone controlling a wallet that holds $200 worth of Ethereum couldn’t resist the opportunity to chime in on Friday. In an on-chain message to Drift’s wallet, the individual wagered that the attackers could “send me $10 million to mess with the Drift team.”
Daily Debrief Newsletter
Start every day with the top news stories right now, plus original features, a podcast, videos and more.
Sign in to highlight and annotate this article

Conversation starters
Daily AI Digest
Get the top 5 AI stories delivered to your inbox every morning.
More about
koreaKnowledge Map
Connected Articles — Knowledge Graph
This article is connected to other articles through shared AI topics and tags.
More in Countries
MEDIA ADVISORY: Subcommittee Hearing on National Security Risks Posed by PRC Artificial Intelligence, Robotics, and Autonomous Technologies – Committee on Homeland Security - House Homeland Security Committee (.gov)
MEDIA ADVISORY: Subcommittee Hearing on National Security Risks Posed by PRC Artificial Intelligence, Robotics, and Autonomous Technologies – Committee on Homeland Security House Homeland Security Committee (.gov)
What next for the struggling rural mothers in China who helped to build AI?
Before autonomous driving freed up the hands of Beijing’s middle class, thousands of workers some 1,500km (930 miles) away in China’s southwestern Guizhou province clicked away at computer screens to teach AI about navigating traffic. In the mountainous city of Tongren, where incomes are less than half those in Beijing, the work of data labelling – marking residential buildings, pavements, roadways and traffic lights – shaped the artificial intelligence guiding those vehicles. The job required...




Discussion
Sign in to join the discussion
No comments yet — be the first to share your thoughts!