Mistral’s $830M AI bet shakes Europe - MSN
<a href="https://news.google.com/rss/articles/CBMiwwFBVV95cUxQTE1mWmRNdWYzV2c3SWYzcm1GNXdiZ1A0ZW1NenJfd203TFYtMkZVMkJfcHJjbVEwMGJoLUVEZnUxVUl3ZnRJbnZzOVdLc1M4RXJhNDJNbjJhdTM4VjdLbTZOTlQ2c3BCdklwekxSOUNjSGVMd18weHd1blRmUUtVc3hIU3ZwVllDTnF1REwyVGJGcnZHWURFT1FMUUlNNGJaQ3JHMnQ4aVdnU0ZFZnlFU253QmV1SHdzbnRDV19TclZBaXM?oc=5" target="_blank">Mistral’s $830M AI bet shakes Europe</a> <font color="#6f6f6f">MSN</font>
Could not retrieve the full article text.
Read on Google News - Mistral AI France →Sign in to highlight and annotate this article

Conversation starters
Daily AI Digest
Get the top 5 AI stories delivered to your inbox every morning.
More about
mistraleurope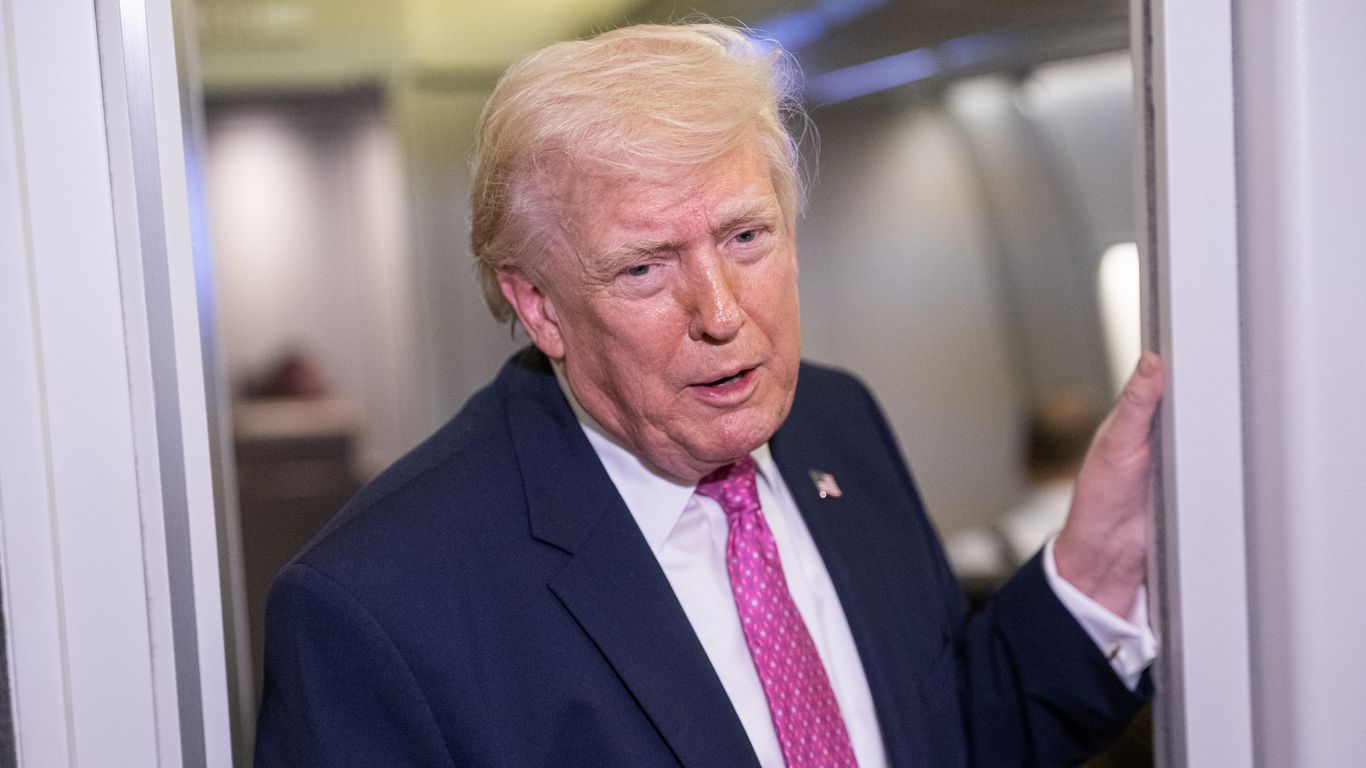
Trump claims Iran asked U.S. for ceasefire
<p>President Trump claimed <a href="https://www.axios.com/world/iran" target="_blank">Iran</a> asked the U.S. for a ceasefire, but stressed he will consider it only if the Strait of Hormuz is reopened. </p><p><strong>Why it matters:</strong> The Iranian regime hasn't confirmed that and has dismissed many of Trump's previous claims of progress towards a deal. </p><hr><ul><li>While Iran and the U.S. have been communicating through mediators, Tehran denies there are any direct talks with the Trump administration.</li><li>Trump might be referring to a statement Iranian President Masoud Pezeshkian made on Tuesday during a call with European Council President António Costa. </li><li>Pezeshkian said Iran was willing to end the war but only if the U.S. stopped its attacks and Iran received guarant

I built a self-hosted RAG system that actually works — here's how to run it in one command
<p>I'll be honest: I spent weeks trying to make existing RAG tools work for my use case. AnythingLLM kept needing cloud APIs. RAGFlow was hard to self-host cleanly. Perplexity-style tools were completely off the table for anything with sensitive documents.</p> <p>So I built my own.</p> <p><strong>RAG Enterprise</strong> is a 100% local RAG system — no data leaves your server, no external APIs, no hidden telemetry. It runs on your hardware with a single setup script. Here's how to get it running.</p> <h2> Why another RAG tool? </h2> <p>Because my clients have real constraints:</p> <ul> <li>Legal documents that can't touch US servers (hello, GDPR)</li> <li>IT departments that won't approve "just use OpenAI" </li> <li>Budgets that don't include $500/month SaaS subscriptions</li> </ul> <p>I ne

How a small German state's bid to replace Microsoft with open-source alternatives like Linux and Kamailio faces issues, as the EU pushes "digital sovereignty" (Laura Pitel/Financial Times)
Laura Pitel / Financial Times : How a small German state's bid to replace Microsoft with open-source alternatives like Linux and Kamailio faces issues, as the EU pushes “digital sovereignty” — Schleswig-Holstein's radical tech overhaul offers Europe a live experiment in ending dependence on US Big Tech
Knowledge Map
Connected Articles — Knowledge Graph
This article is connected to other articles through shared AI topics and tags.
More in Models

Semantic Labeling for Third-Party Cybersecurity Risk Assessment: A Semi-Supervised Approach to Intent-Aware Question Retrieval
arXiv:2602.10149v3 Announce Type: replace Abstract: Third-Party Risk Assessment (TPRA) relies on large repositories of cybersecurity compliance questions used to assess external suppliers against standards such as ISO/IEC 27001 and NIST. In practice, not all questions are relevant for a specific supplier and selecting questions for a given assessment context remains a manual and time-consuming task. Existing question retrieval approaches based on lexical or semantic similarity can identify topically related questions, but they often fail to capture the underlying assessment intent, including control domain and evaluation scope. To address this limitation, we investigate whether an explicit semantic label space can improve intent-aware TPRA question selection. In particular, we separate lab

DUAP: Dual-task Universal Adversarial Perturbations Against Voice Control Systems
arXiv:2601.12786v2 Announce Type: replace Abstract: Modern Voice Control Systems (VCS) rely on the collaboration of Automatic Speech Recognition (ASR) and Speaker Recognition (SR) for secure interaction. However, prior adversarial attacks typically target these tasks in isolation, overlooking the coupled decision pipeline in real-world scenarios. Consequently, single-task attacks often fail to pose a practical threat. To fill this gap, we first utilize gradient analysis to reveal that ASR and SR exhibit no inherent conflicts. Building on this, we propose Dual-task Universal Adversarial Perturbation (DUAP). Specifically, DUAP employs a targeted surrogate objective to effectively disrupt ASR transcription and introduces a Dynamic Normalized Ensemble (DNE) strategy to enhance transferability

LaSM: Layer-wise Scaling Mechanism for Defending Pop-up Attack on GUI Agents
arXiv:2507.10610v2 Announce Type: replace Abstract: Graphical user interface (GUI) agents built on multimodal large language models (MLLMs) have recently demonstrated strong decision-making abilities in screen-based interaction tasks. However, they remain highly vulnerable to pop-up-based environmental injection attacks, where malicious visual elements divert model attention and lead to unsafe or incorrect actions. Existing defense methods either require costly retraining or perform poorly under inductive interference. In this work, we systematically study how such attacks alter the attention behavior of GUI agents and uncover a layer-wise attention divergence pattern between correct and incorrect outputs. Based on this insight, we propose \textbf{LaSM}, a \textit{Layer-wise Scaling Mechan

SHIFT: Stochastic Hidden-Trajectory Deflection for Removing Diffusion-based Watermark
arXiv:2603.29742v1 Announce Type: cross Abstract: Diffusion-based watermarking methods embed verifiable marks by manipulating the initial noise or the reverse diffusion trajectory. However, these methods share a critical assumption: verification can succeed only if the diffusion trajectory can be faithfully reconstructed. This reliance on trajectory recovery constitutes a fundamental and exploitable vulnerability. We propose $\underline{\mathbf{S}}$tochastic $\underline{\mathbf{Hi}}$dden-Trajectory De$\underline{\mathbf{f}}$lec$\underline{\mathbf{t}}$ion ($\mathbf{SHIFT}$), a training-free attack that exploits this common weakness across diverse watermarking paradigms. SHIFT leverages stochastic diffusion resampling to deflect the generative trajectory in latent space, making the reconstru
Discussion
Sign in to join the discussion
No comments yet — be the first to share your thoughts!