Scaling Trust: How Salesforce s Security Team Uses Agentforce to Triage Security Reports at Speed
By Kelly McCracken and Raaghavv Devgon. In our Engineering Energizers Q A series, we highlight the engineering minds driving innovation across Salesforce. Today, we spotlight Kelly McCracken, Senior Vice President of Information Security, whose Cyber Security Operations Center team built an AI-driven security system using Agentforce to triage and respond to customer-reported vulnerability findings at scale, [ ] The post Scaling Trust: How Salesforce s Security Team Uses Agentforce to Triage Security Reports at Speed appeared first on Salesforce Engineering Blog .
By Kelly McCracken and Raaghavv Devgon.
In our Engineering Energizers Q&A series, we highlight the engineering minds driving innovation across Salesforce. Today, we spotlight Kelly McCracken, Senior Vice President of Information Security, whose Cyber Security Operations Center team built an AI-driven security system using Agentforce to triage and respond to customer-reported vulnerability findings at scale, successfully managing a 30% increase in report volume year over year without expanding their team.
Explore how Kelly’s team addressed the challenge of ingesting highly unstructured vulnerability reports across diverse formats while correctly identifying the relevant product across a large portfolio, and managing rapidly increasing report volume without expanding the team and meeting strict response time requirements.
What is your team’s mission as it relates to building the product vulnerability response agent?
The team operates a security model designed to detect and analyze threats across all environments with speed and consistency. To support this mission, the team built a product vulnerability response agent to handle security findings reported by third-party researchers and assessments.
This agent functions as an AI-assisted triage system that analyzes incoming reports to determine if a finding represents a real issue or expected behavior. It then generates recommended responses for security engineers, moving the team away from a fully manual model toward an accelerated workflow.
By embedding this agent into the process, engineers retain final decision-making authority while scaling their ability to respond to increasing report volumes. This approach ensures the team maintains response requirements and addresses customer concerns accurately.
What challenges shaped how the product vulnerability response agent ingests unstructured vulnerability reports and correctly identifies the relevant product across a large and diverse portfolio?
The variability and density of incoming vulnerability reports can pose many challenges. Customers submit findings in multiple formats, such as PDFs, spreadsheets, and security tool outputs. These reports often contain complex diagrams and machine-generated data, which often requires significant time to parse manually.
To address this, the team built a format-agnostic approach that extracts meaningful signals across these different structures. However, the system also needed to identify the correct product within a large portfolio of SaaS and on-premises offerings. Early versions lacked this specific context, which limited the accuracy of their recommendations.
The team solved these issues by using Agentforce to process diverse inputs and by introducing parsing logic. This logic infers product context, allowing the system to align reports with the correct product knowledge and generate accurate triage recommendations.
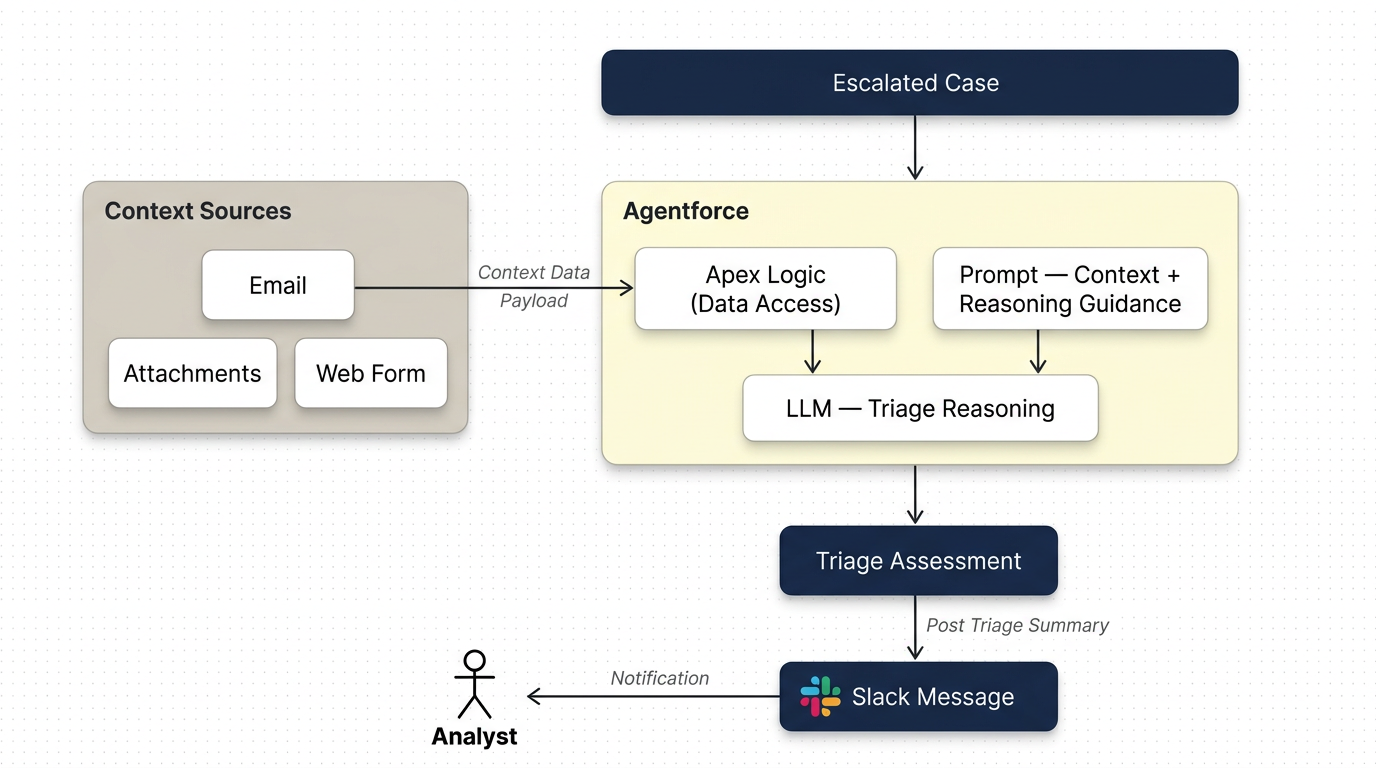
Workflow of a product vulnerability report being processed by the Product Vulnerability Response Agent.
What scalability constraints emerged as vulnerability report volume increased alongside Salesforce’s growing customer base?
Salesforce growth led to a direct increase in potential vulnerability report submissions as more customers conducted third-party assessments. This surge created a scaling challenge where the workload grew significantly without a corresponding increase in team size, placing pressure on response times.
The team designed the system to absorb this growth by automating key parts of the triage workflow. This allowed the team to handle a 30% increase in reports over one year without adding headcount while still meeting response commitments.
A critical improvement came from eliminating delays in routing and initial analysis. The system completes routing and initial triage in seconds, allowing analysis to start immediately and reducing end-to-end response times.
What challenges did the team face ensuring vulnerability reports contained the structured data required for accurate triage?
Inconsistent and incomplete reports submitted via email created a significant bottleneck for the team. Many submissions lacked reproducible steps or sufficient context, forcing analysts to spend time following up with reporters before triage could begin.
In response, we replaced unstructured emails with a web-based interface and structured reporting workflows. This new form enforces the inclusion of required data fields to ensure every report contains the information needed for immediate analysis.
Standardizing inputs at the point of submission improved data quality and processing efficiency. The system now begins analysis without waiting for additional clarification, which reduces back-and-forth communication and accelerates the triage lifecycle.
What architectural decisions shaped how the product vulnerability response agent generates triage recommendations and integrates into analyst workflows?
The team integrated the system directly into Slack to ensure recommendations and analysis occur within existing workflows. This approach avoids the need for a separate interface and reduces friction for security engineers. By functioning as a collaborative participant, the system improves adoption across the organization.
The architecture emphasizes a human-in-the-loop model where the system generates triage recommendations while security engineers retain final decision authority. This structure accelerates workflows and maintains high standards for accuracy.
This integration also enables continuous learning. Analysts provide feedback directly within the workflow, which allows the system to improve over time based on real usage patterns.
What challenges did the team face ensuring the product vulnerability response agent can accurately distinguish real vulnerabilities from expected product behavior?
Distinguishing between true vulnerabilities and expected behavior remains a complex challenge for security systems. Many reports describe scenarios that appear to be security issues but actually function as designed. In response, the team built a comprehensive knowledge foundation that goes beyond surface-level analysis.
The system achieved over 90% accuracy in initial triage. It also identifies cases where confidence is low to signal the need for human review. By combining a structured knowledge base with human validation, the team created a system that produces reliable recommendations and maintains trust in security decisions.
Learn more
-
Stay connected — join our Talent Community!
-
Check out our Technology and Product teams to learn how you can get involved.
engineering.salesforce.com
https://engineering.salesforce.com/scaling-trust-how-salesforces-security-team-uses-agentforce-to-triage-security-reports-at-speed/Sign in to highlight and annotate this article

Conversation starters
Daily AI Digest
Get the top 5 AI stories delivered to your inbox every morning.
More about
reportagentfindings
Digital Project Abandonment Crisis: Deadweight Loss in Plain Sight
The most cited figure in startup failure research comes from the U.S. Bureau of Labor Statistics: roughly 20% of businesses fail in their first year, and about 65% within ten years. For technology companies specifically, CB Insights' analysis of over 110 startup post-mortems found that 42% failed because there was no genuine market need for what they built. Running out of cash was second at 29% — but as the report noted, cash problems typically trail the market need problem by months. The technology sector fails at higher rates than the broader business population. Approximately 63% of tech businesses fail within five years. For software-as-a-service companies specifically, the dynamics are similar: roughly 90% of SaaS startups fail to reach sustainable scale. None of these numbers are enc
Knowledge Map
Connected Articles — Knowledge Graph
This article is connected to other articles through shared AI topics and tags.
More in Products

What happens when you give an AI your acceptance criteria and ask it to write test cases?
After years of building frontend applications across e-health and e-learning products, I've sat in enough sprint reviews to notice a pattern: QA test cases are written the same way every time. Happy path first, a handful of negative cases if the deadline allows, edge cases if the tester has seen that bug before. The process is repetitive, experience-dependent, and the first thing to get cut when a release is running late. So I started experimenting — feeding acceptance criteria directly to an AI and asking for a complete test suite. Here's an honest account of what works, what doesn't, and what it actually changes about the process. What the AI gets right immediately The output quality on structured coverage is genuinely impressive. Given clear acceptance criteria, the AI will produce happ

Self-Hosting in 2026: Why It Matters and How to Get Started
Every year, another SaaS tool raises prices, removes features, or shuts down. Your monthly stack — file storage, password management, project tracking, monitoring, analytics, automation — keeps growing. So does the bill. Self-hosting is the alternative. Run the software on your own server, keep your data under your control, and stop paying per-seat fees for tools that are free and open-source. Docker made deployment trivial. Open-source alternatives have matured to rival their commercial counterparts. And a $4–20/month VPS gives you enough compute to run a full stack. Self-hosting in 2026 isn't a niche hobby — it's a practical strategy. What Self-Hosting Means in Practice You install and run applications on a server you control. Your files, passwords, analytics, and workflows stay on your

Built a Lightweight GitHub Action for Deploying to Azure Static Web Apps
TL;DR I created shibayan/swa-deploy — a lightweight GitHub Action that only deploys to Azure Static Web Apps, without the Docker-based build overhead of the official action. It wraps the same StaticSitesClient that SWA CLI uses internally, includes automatic caching, and supports both Deployment Token and azure/login authentication. The Problem with the Official Action When deploying static sites (built with Astro, Vite, etc.) to Azure Static Web Apps, the standard approach is to use the official Azure/static-web-apps-deploy action that gets auto-generated when you link a GitHub repo to your SWA resource. Unlike other Azure deployment actions (e.g., for App Service or Azure Functions), this action uses Oryx — the build engine used across Azure App Service — to build your application intern

Defining and creating a basic Design System based on any website (in Figma and React) using Claude
It's 2026, and MCP and design tooling are constantly changing with various improvements in the AI space. Arguably, one of the most long-awaited features was Figma MCP supporting agents writing to its canvas. The funny thing is, I created a particular workflow 2 weeks ago, the lack of the write to canvas was a bit of a bottleneck but could be worked around since Claude Code was pretty good at generating plugins to create and clean up tokens (variables), as well as components and their props. Thankfully, that gap didn't hang around for long enough, and now there's native support for writing directly to canvas. Firstly, we'll look at how we can set up the correct tooling for the following use case: You've joined a startup, they have a website or a web page, but lack any reusable design system

Discussion
Sign in to join the discussion
No comments yet — be the first to share your thoughts!