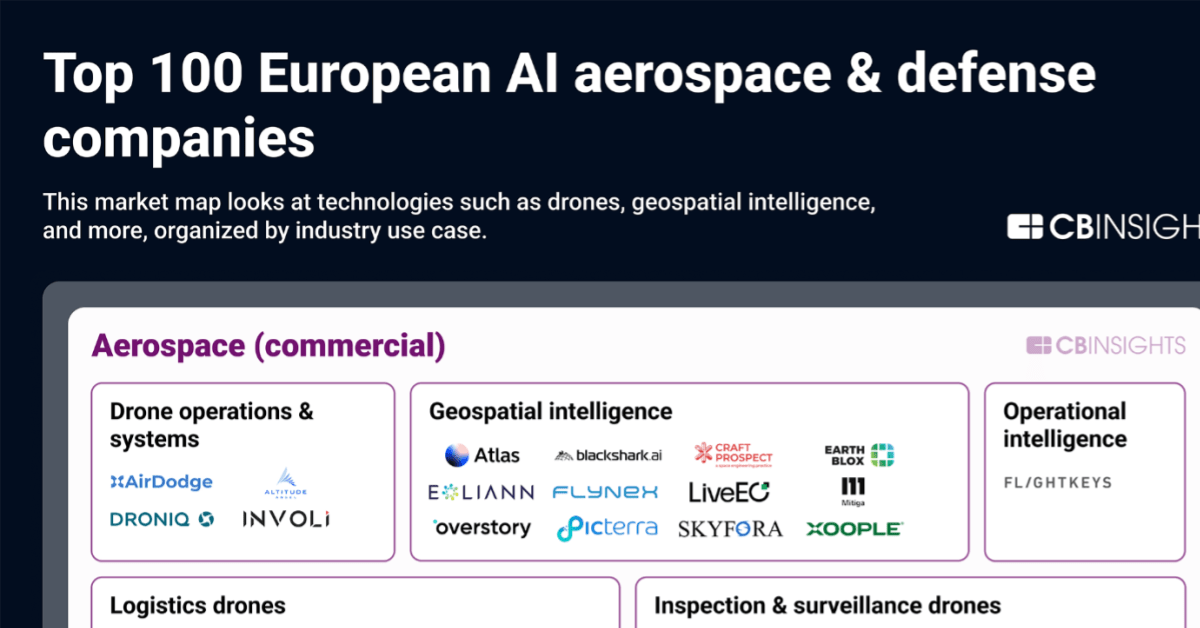
The top 100 European AI aerospace & defense startups
Geopolitical events are driving Europe to strengthen its independence in aerospace and defense, particularly in AI capabilities traditionally dominated by the US, such as drones, autonomous ground robots, and intelligence platforms. The conflict in Ukraine demonstrates the significant impact of … The post The top 100 European AI aerospace & defense startups appeared first on CB Insights Research .
Geopolitical events are driving Europe to strengthen its independence in aerospace and defense, particularly in AI capabilities traditionally dominated by the US, such as drones, autonomous ground robots, and intelligence platforms.
The conflict in Ukraine demonstrates the significant impact of these technologies — think low-cost drones destroying $5M tanks — driving European investment in domestic defense systems and supply chains.
Beyond defense, European startups are also deploying AI-powered systems across commercial sectors, helping capture new markets and build independence from foreign suppliers.
CB Insights Research
https://www.cbinsights.com/research/the-top-100-european-ai-aerospace-defense-startups/Sign in to highlight and annotate this article

Conversation starters
Daily AI Digest
Get the top 5 AI stories delivered to your inbox every morning.
More about
platformstartupinsight
How to Hyper-Personalization in Action: From Story Angle to Ranked Media List in Minutes
Title: Beyond the Blast: Using AI to Hyper-Personalize Media Lists Intro: You’ve spent hours crafting a perfect story angle. Now, you face the tedious, error-prone task of matching it to the right journalists. Generic lists lead to ignored pitches. AI automation turns this from a chore into a strategic advantage. Core Principle: Contextual Matching Over Keyword Spraying The key is to move beyond simple keyword matching (“climate tech”) to contextual alignment. AI can analyze a journalist’s entire body of work—their recent focus, narrative style, and even subtle tone preferences—to judge true fit for your specific angle. This ensures your pitch lands in an inbox already primed for your story’s theme. Tool in Action: An AI-Augmented Media Database Imagine a platform like Meltwater’s AI tools

How to Scrape DoorDash, Uber Eats, and Grubhub Menu Data in 2026
How to Scrape DoorDash, Uber Eats, and Grubhub Menu Data in 2026 Food delivery platforms are among the harder scraping targets — they use aggressive anti-bot measures, require location parameters, and structure their data differently across platforms. Here's what actually works for extracting menu data, restaurant listings, and pricing. DoorDash: Menu Data Extraction DoorDash embeds menu data in the page's server-side rendered HTML as a JSON blob. This is the cleanest approach — no API authentication needed: import requests , re , json from curl_cffi import requests as cf_requests def scrape_doordash_menu ( store_url : str ) -> dict : """ Extract menu data from a DoorDash restaurant page. URL format: https://www.doordash.com/store/restaurant-name-city-12345/ """ session = cf_requests . Ses

GHSA-QCC3-JQWP-5VH2: GHSA-qcc3-jqwp-5vh2: Unauthenticated Resource Exhaustion via LINE Webhook Handler in OpenClaw
GHSA-qcc3-jqwp-5vh2: Unauthenticated Resource Exhaustion via LINE Webhook Handler in OpenClaw Vulnerability ID: GHSA-QCC3-JQWP-5VH2 CVSS Score: 5.3 Published: 2026-04-02 The OpenClaw personal AI assistant platform contains a resource exhaustion vulnerability in its LINE webhook handler. The application fails to enforce concurrency limits prior to processing unauthenticated HTTP POST requests, allowing an attacker to cause a Denial of Service (DoS) through rapid CPU and memory consumption. TL;DR Unauthenticated attackers can trigger severe Denial of Service in OpenClaw by sending high-concurrency requests to the LINE webhook handler. The lack of a pre-authentication resource budget causes the server to exhaust memory and CPU while performing cryptographic signature verification. Technical D
Knowledge Map
Connected Articles — Knowledge Graph
This article is connected to other articles through shared AI topics and tags.
More in Products

AWS Red Teaming Assessment
AWS Cloud Red Team Assessment Table of Contents Authorization Legal Scope Definition Methodology Attack Scenarios Technical Commands MITRE ATT CK Mapping Risk Assessment Remediation Recommendations Detection Engineering Appendix 1. Authorization Legal 1.1 AWS Penetration Testing Policy AWS allows customers to conduct penetration testing on their own AWS infrastructure without prior approval, subject to the following conditions: ✅ Permitted Activities: Penetration testing against AWS resources you own Security assessments of EC2, RDS, Lambda, S3, and other AWS services Vulnerability scanning of your own applications Social engineering campaigns against your employees Physical security testing of your own facilities ❌ Prohibited Activities: DNS zone walking via Route 53 AWS service availabil

Reverse Engineering Cloudflare's React-Based Bot Detection in 2026
Reverse Engineering Cloudflare's React-Based Bot Detection in 2026 Some sites protected by Cloudflare now embed their bot detection logic inside React components rather than a separate challenge page. This is harder to bypass because the detection happens inline — inside the same React render cycle as the content you want — rather than as a clear challenge/pass gate. Here's how it works and what you can do about it. How React-Based Cloudflare Detection Works Traditional Cloudflare protection intercepts requests at the CDN level and presents a challenge page before the target site loads. React-based detection is different: The CDN serves the React app with no challenge The React app renders and executes JavaScript Inside a React component (often an useEffect hook), Cloudflare's bot detectio

How to Hyper-Personalization in Action: From Story Angle to Ranked Media List in Minutes
Title: Beyond the Blast: Using AI to Hyper-Personalize Media Lists Intro: You’ve spent hours crafting a perfect story angle. Now, you face the tedious, error-prone task of matching it to the right journalists. Generic lists lead to ignored pitches. AI automation turns this from a chore into a strategic advantage. Core Principle: Contextual Matching Over Keyword Spraying The key is to move beyond simple keyword matching (“climate tech”) to contextual alignment. AI can analyze a journalist’s entire body of work—their recent focus, narrative style, and even subtle tone preferences—to judge true fit for your specific angle. This ensures your pitch lands in an inbox already primed for your story’s theme. Tool in Action: An AI-Augmented Media Database Imagine a platform like Meltwater’s AI tools

How to Scrape DoorDash, Uber Eats, and Grubhub Menu Data in 2026
How to Scrape DoorDash, Uber Eats, and Grubhub Menu Data in 2026 Food delivery platforms are among the harder scraping targets — they use aggressive anti-bot measures, require location parameters, and structure their data differently across platforms. Here's what actually works for extracting menu data, restaurant listings, and pricing. DoorDash: Menu Data Extraction DoorDash embeds menu data in the page's server-side rendered HTML as a JSON blob. This is the cleanest approach — no API authentication needed: import requests , re , json from curl_cffi import requests as cf_requests def scrape_doordash_menu ( store_url : str ) -> dict : """ Extract menu data from a DoorDash restaurant page. URL format: https://www.doordash.com/store/restaurant-name-city-12345/ """ session = cf_requests . Ses

Discussion
Sign in to join the discussion
No comments yet — be the first to share your thoughts!