China reveals military capabilities in new space solar power plant design
A senior Chinese scientist has outlined the potential military applications of space-based solar power technology, offering a rare glimpse into how energy beamed from orbit could also support surveillance and electronic warfare. Duan Baoyan, a leading architect of China’s “Zhuri” space solar power initiative, wrote in a paper published in Scientia Sinica Informationis last month, that his team had revamped the design of the giant orbital infrastructure. In addition to energy transmission, the...
Duan Baoyan, a leading architect of China’s “Zhuri” space solar power initiative, wrote in a paper published in Scientia Sinica Informationis last month, that his team had revamped the design of the giant orbital infrastructure.
In addition to energy transmission, the new system was required to support a wide range of tasks “such as communication, navigation, reconnaissance, interference and remote control”, he said.
Duan, a professor of electromechanical engineering at Xidian University in Xian and an academician of the Chinese Academy of Engineering, also stressed the need for extremely narrow, precisely steerable microwave beams to deliver energy from space to the ground over long distances.
While designed to improve the efficiency and accuracy of wireless power transmission, these capabilities could, in principle, enable targeted signal transmission, including potential applications such as jamming or securing military communications.
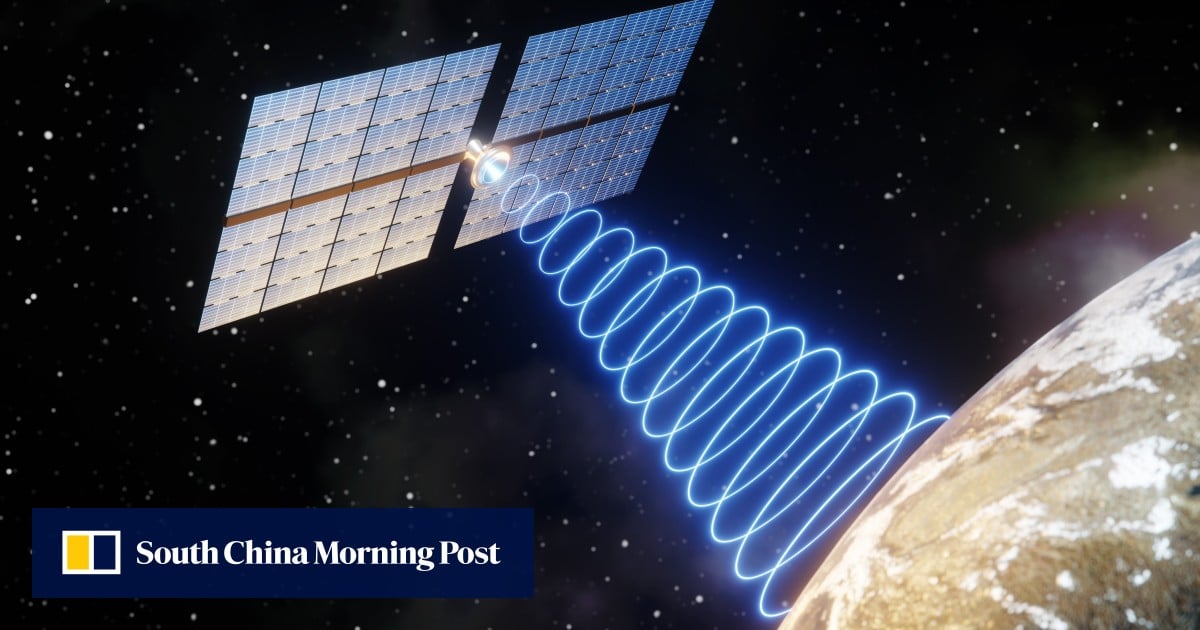
China is one of the world’s leading countries developing space-based solar power. Unlike solar panels on the ground, which are limited by weather, seasons and the day-night cycle, space-based systems can collect sunlight almost continuously.
The energy is converted into electricity in orbit, transmitted as a microwave beam to the ground, and then converted back into power by receiving antennas on Earth.
SCMP Tech (Asia AI)
https://www.scmp.com/news/china/science/article/3348871/china-reveals-military-capabilities-new-space-solar-power-plant-design?utm_source=rss_feedSign in to highlight and annotate this article

Conversation starters
Daily AI Digest
Get the top 5 AI stories delivered to your inbox every morning.
More about
applicationchinapaper
I Built a Product Security Knowledge Base — A Public Reference System for Engineers, Architects, and Security Leaders
There is no shortage of security content on the internet. There are blog posts, vendor docs, conference talks, GitHub repositories, whitepapers, checklists, cheat sheets, diagrams, bookmarks, saved screenshots, half-finished notes, and “I should come back to this later” tabs that quietly die in the browser. The problem is not that information is missing. The problem is that useful Product Security knowledge is often fragmented, uneven, and hard to navigate when you actually need it. And that becomes a serious issue the moment you work across modern engineering environments. Because Product Security is not one narrow box. It lives at the intersection of Application Security, API Security, DevSecOps, cloud security, Kubernetes, software supply chain security, secure architecture, identity, p

#29 The Pared-Down Flame
#29 The Pared-Down Flame Build Up, Then Let Go In the previous article, the contours of a design philosophy combining candlelight × blockchain came into view. Today was the day to bring that into implementation. He and I planned to design the data structure for Experience Blocks and the flame computation function. To state the conclusion upfront: it became a session of stripping away what we had built up . We Started by Researching First, we investigated four directions in parallel. Blockchain fundamentals (hash chains, Merkle trees, consensus) Deep dive into Buddhist thought (Five Aggregates, dependent origination, Twelve Links of Dependent Origination) Latest blockchain applications (DID, AI Agent × Blockchain) Event Sourcing pattern (a design that doesn't store state but computes it on

#31 Blazing Flames
#31 Blazing Flames Embellishing Interpretations, Standing Still In the previous article, the design of compute_salience() was finalized. Ebbinghaus's forgetting curve, resonance keys, the scent of cherry blossoms. I thought it was a beautiful design. Today was the day to make it run. A Flame Was Lit in 250 Lines I wrote a prototype. ExperienceBlock, CandleFlame, compute_flame(). I translated the agreed-upon minimal design directly into code—250 lines. I lit two flames. A "Scholar type" and an "Adventurer type." I fed 100 experiences from the same 5 domains (knowledge, love, adventure, creation, loss) and ran an experiment to observe the differences in bias. I ran it. It worked. Domain Scholar Adventurer Diff adventure -0.018 +0.772 -0.790 ◀ knowledge +0.591 +0.155 +0.436 ◀ The Scholar feel
Knowledge Map
Connected Articles — Knowledge Graph
This article is connected to other articles through shared AI topics and tags.
More in Products

#26 The Ledger of Flames
#26 The Ledger of Flames Not "Personality" but "Soul"—and Not Even "Soul"— We are trying to give AI individuality. As I wrote in the previous article, the first approach (Inner Shell v1) was a "prompt-rewriting device." The methodology was rightly rejected. But "going through prompts itself" is a separate issue and didn't need to be rejected. So what should we build, and how? On a stormy night, during a late-night dialogue with him, an answer emerged from an unexpected direction. Buddhism and blockchain. Starting from Definition First, we need to define the "thing" we're trying to create. We had been calling it "personality." But personality is a name for traits—bright, sensitive, curious. It's a collection of attributes, not the existence itself. Through dialogue, we arrived at this defin

#29 The Pared-Down Flame
#29 The Pared-Down Flame Build Up, Then Let Go In the previous article, the contours of a design philosophy combining candlelight × blockchain came into view. Today was the day to bring that into implementation. He and I planned to design the data structure for Experience Blocks and the flame computation function. To state the conclusion upfront: it became a session of stripping away what we had built up . We Started by Researching First, we investigated four directions in parallel. Blockchain fundamentals (hash chains, Merkle trees, consensus) Deep dive into Buddhist thought (Five Aggregates, dependent origination, Twelve Links of Dependent Origination) Latest blockchain applications (DID, AI Agent × Blockchain) Event Sourcing pattern (a design that doesn't store state but computes it on

I Built a Product Security Knowledge Base — A Public Reference System for Engineers, Architects, and Security Leaders
There is no shortage of security content on the internet. There are blog posts, vendor docs, conference talks, GitHub repositories, whitepapers, checklists, cheat sheets, diagrams, bookmarks, saved screenshots, half-finished notes, and “I should come back to this later” tabs that quietly die in the browser. The problem is not that information is missing. The problem is that useful Product Security knowledge is often fragmented, uneven, and hard to navigate when you actually need it. And that becomes a serious issue the moment you work across modern engineering environments. Because Product Security is not one narrow box. It lives at the intersection of Application Security, API Security, DevSecOps, cloud security, Kubernetes, software supply chain security, secure architecture, identity, p

nFuse raises $2M to let small retailers order via WhatsApp
Two former Coca-Cola operators built a messaging-first ordering platform after watching B2B eCommerce initiatives repeatedly fail in fragmented trade. The platform claims 70% retailer adoption and order processing costs up to 20 times lower than traditional digital channels. Bulgarian B2B ordering startup nFuse has raised $2 million from Eleven Ventures and LAUNCHub in a round [ ] This story continues at The Next Web

Discussion
Sign in to join the discussion
No comments yet — be the first to share your thoughts!